Attention: Hackers Dropping Malware in Microsoft Team Chats
Apologies if the title is somewhat alarmist, but I wanted to bring your attention to an important cybersecurity issue.
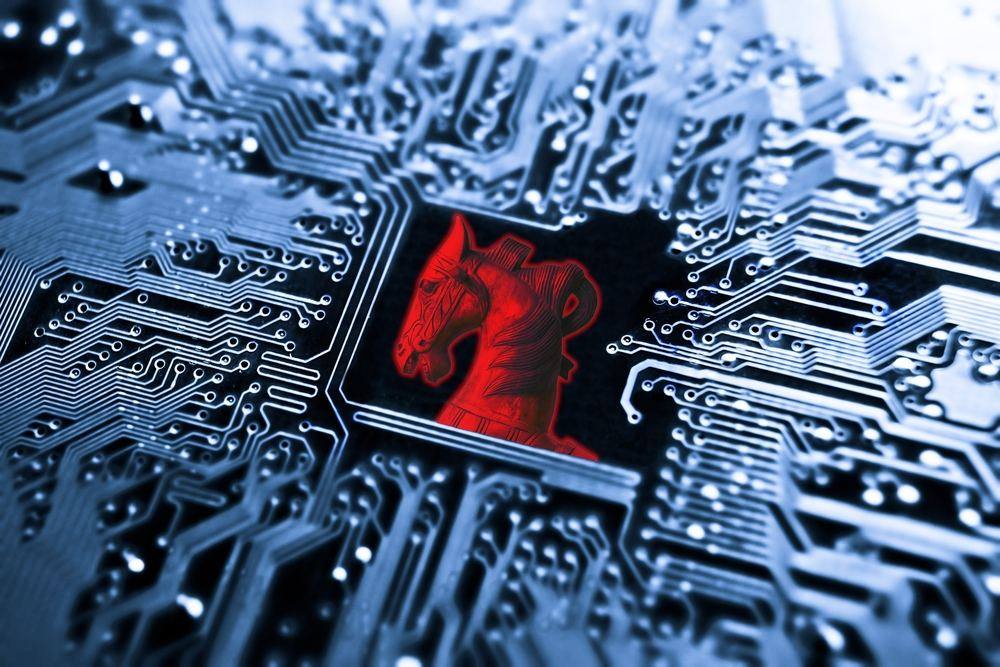
It was recently discovered that malicious actors are dropping malicious malware in Microsoft Teams chats. The malware is a type of Trojan disguised as an executable file labelled “User-Centric”.
The attacks were identified by US company Avanan, a cybersecurity solutions provider that works for governments and corporations. A recent report published by the security firm describes in detail how hackers are dropping malware-infested .exe files labelled “User-Centric” in chat threads on Teams.
Avanan says the attached documents dropped into Team chats appear to be legitimate because they have come through a channel belonging to a trusted source.
Hackers are targeting Microsoft Teams instead of emails because the element of trust is more likely to prompt end-users to open the infected files. Employees know not to trust emails and, in the main, can identify a phishing attack.

When the “User-Centric” files are opened, however, malicious malware is installed in the library of the end-users computer. It’s quite easy for hackers to create scripts that can be installed into a Windows service folder without being easily detected.
According to Avanan, threat actors may be using Microsoft 365 credentials sourced from earlier phishing campaigns. Because of the wide use of Microsoft Teams, millions of businesses in the UK could be at risk of a data breach.
Given the “User-Centric” malware in Microsoft Teams is a new technique, there is a strong likelihood that the malicious code will also be unique. Subsequently, existing anti-virus software may not be able to identify it.
This appears to be the case. According to pcmag.com:
“Microsoft didn’t immediately respond to a request for comment. However, a company support document says Microsoft Teams does have a built-in antivirus detection through Microsoft 365, although Avanan claimed the scanning was still limited, and slow to identify attacks in real-time.”
We recommend that all Microsoft Team users take the following steps:
- Ensure you have a robust and unique password, change your password if they are not.
- Don’t open any attachments in Teams unless you expected it, and have verified it has been sent by a colleague or trusted client
- Before opening an attached file, hover your mouse over the file. If the link has “User-Centric” in the description, alert a member of your IT security staff to quarantine the file.
- If you suspect your computer is infected shut it down and inform your IT support team.
- Notify staff and IT of existing suspicious activity immediately
- Educate your team that Microsoft Teams can be a vector for attacks, and like anything else involving a computer, all actions taken should be given ample consideration.
How does a business network get infected with malicious malware?
Malicious malware is a type of computer virus that hackers use to infiltrate business networks. Malware can spy on the activity of a computer user or take over the computer to perform egregious actions.
Malware comes in various forms. Some of the most common are Trojan horses, worms, spyware and ransomware. The malicious code is programmed into infected files that when opened is automatically installed onto the victim’s computer or mobile device.

Most malware is “DLL files” – a set of code and data for carrying out a particular activity in Windows. Once the program is installed into a computer’s library, hackers can take over your computer and execute spoofing campaigns.
This is how threat actors are attaching documents infected with malicious malware in Microsoft Teams chats.
IT Security Consultancy and Support
The consistent threat of cyberattacks means that businesses of all sizes are at risk. SMEs are arguably the most vulnerable cohort of businesses because of the costs involved following a data breach.
Not only that but under the rules of GDPR, you are obligated to inform all parties that may have been affected by a data breach. The damage hackers can cause to your reputation could put you out of business.
Cybersecurity, then, becomes a business-critical strategy. And because the tools and techniques used by hackers are constantly evolving, IT security teams need to look for ways of defending business networks and ensuring you have access to skilled IT personnel that have in-depth knowledge and experience in building cybersecurity infrastructure.
The approach we take to cybersecurity at Micro Pro depends on your business needs. If you have an existing team of IT professionals that have some experience with cybersecurity defences, our top-level directors can simply act as consultants.
Our highly experienced and knowledgeable consultants will analyse your existing security framework and make recommendations to make your cybersecurity defences as tight as it can be. We also review your compliance obligations to ensure you are meeting international standards.
It’s worth bearing in mind that one in five data breaches are the result of misconfigured cloud software. If you’re using cloud computing, we highly recommend utilising the expertise of experienced cloud technicians.
Firms that have resisted migrating to the cloud may even want to re-evaluate their storage strategy. Cloud computing can be used to add extra layers of cybersecurity to your network defences.
Storing and backing up data in the cloud is also retrievable, so provides a solution that enables you to avoid paying hackers a ransom to give you access to your files.
Our IT security specialists can also help you build, install and execute a cybersecurity strategy. If required, we can also educate your staff members on the latest social engineering techniques hackers are using – such as the “User-Centric” malware discovered in Microsoft Teams.
If would also like ongoing support, we use advanced remote monitoring software to identify threats before they become a problem. Cybersecurity solutions include encryption, anti-virus checks, multi-factor authentication and patch management.
Don’t risk leaving your business network open for hackers to exploit. Contact Micro Pro today and stay protected. Our IT professionals in London, Surrey,
Kent and Glasgow are here to help, and with an award-winning helpdesk team at your service 24/7, your team can reach out to us anytime, and from anywhere.